Overview
The global cyber threat continues to evolve at a rapid pace, with a rising number of data breaches each year. NTPL has expertise in Cyber security, Vulnerability Assessment, SAST and DAST.
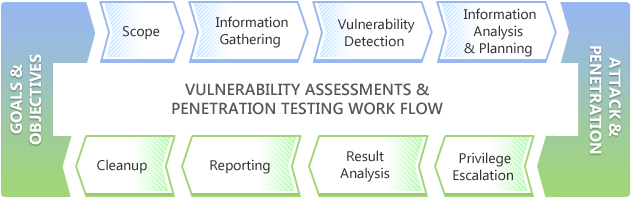
We are delivering comprehensive security solutions and services. We adopt an end-to-end security Automation Testing approach from information congregation to result in reporting for uncovering the vulnerabilities, Mitigating the security risks and enhancing the security posture of the applications and Cyber security products.
While vulnerability assessment and remediation is used to strengthen the computer systems, it is also important to perform suitable penetration tests periodically to identify the possibilities of system compromise. The primary purpose of penetration tests is to identify the exploitation of a vulnerability.


Our Offerings
Application Security
- Expertise in Static and Dynamic Application Testing (SAST & DAST) using Secure Code Review framework and tools
VA/PT
- Expertise In Vulnerability Assessment and Penetration Testing tools such as BurpSuite, Zap.
SIEM - SOC
- Experience in Setting up and Managing SOC (Security Operations Center) from Offshore for Japanese Clients covering Helpdesk, L1 and L2 Activities. Expertise In SIEM tools such As Splunk, Arcsight.
Cyber Security
- Expertise In Vulnerability Assessment in Cyber Network Environment using Techniques and tools Such as Metasploit, Kali Linux tools.